16Views 0Comments

How to Avoid Crypto Scams: Protect Your Money Now
The cryptocurrency landscape has transformed from a niche technological experiment into a $2.5 trillion global market, but this explosive growth has attracted sophisticated criminals who have stolen an estimated $4 billion from crypto investors in 2023 alone. As digital assets become mainstream investment vehicles, understanding how to identify and avoid crypto scams has shifted from optional knowledge to essential financial literacy. Whether you’re a seasoned trader or just purchasing your first Bitcoin, the techniques outlined in this guide could mean the difference between building wealth and losing everything to fraud.
Understanding the Crypto Scam Landscape in 2024
The cryptocurrency scam ecosystem has evolved far beyond the crude email phishing attempts of 2017. Today’s fraudsters operate professional operations with sophisticated marketing, fake celebrity endorsements, and convincing customer service representatives who spend weeks building trust before executing their theft. The Federal Trade Commission reported that crypto-related fraud losses exceeded $1.4 billion in 2023, with the average victim losing approximately $3,800. This isn’t random theft—it’s a calculated industry built on psychological manipulation and technical deception.
The most alarming trend is the democratization of scam tools. Dark web marketplaces now sell ready-made Ponzi schemes, fake exchange websites, and fraudulent initial coin offering (ICO) packages for as little as $500. This low barrier to entry means anyone with basic technical knowledge and willingness to commit fraud can launch a crypto scam within days. Meanwhile, legitimate cryptocurrency’s complexity—wallet addresses, private keys, blockchain transactions—creates confusion that scammers exploit brilliantly.
What makes crypto uniquely vulnerable is the irreversible nature of blockchain transactions. Unlike bank transfers that can sometimes be contested or credit card charges that can be disputed, cryptocurrency transactions are final by design. Once your funds leave your wallet to a scammer’s address, recovery is nearly impossible. This permanence attracts criminals who know their victims have zero recourse once the transaction confirms.
The Most Common Crypto Scams Explained
Ponzi Schemes and Investment Clubs
BitConnect, which collapsed in 2018 after defrauding investors of $2 billion, established the template that hundreds of scams have since replicated. These schemes promise guaranteed returns—often 1-3% daily—through proprietary “trading bots” or “arbitrage algorithms” that supposedly generate consistent profits regardless of market conditions. The reality involves paying early investors with money from new participants, a structure that inevitably collapses when recruitment slows.
Modern Ponzi schemes have grown more sophisticated, operating as Telegram groups, Discord servers, or private membership sites where “investment coaches” share tips and celebrate withdrawals. The social proof element is deliberate—seeing others supposedly profit convinces victims to invest more. According to the Blockchain Intelligence Group, investment Ponzi schemes accounted for 34% of all crypto fraud losses in 2023.
Phishing and Identity Theft
Crypto phishing has evolved into a multi-channel operation targeting every touchpoint in the investor journey. Attackers create fake versions of popular exchanges, lending platforms, and wallet interfaces that are nearly indistinguishable from the real sites. When victims enter their login credentials, attackers capture the information and drain associated accounts within minutes.
Beyond website clones, scammers execute targeted attacks through email spoofing, SMS message hijacking (SIM swapping), and social media direct messages. Sophisticated campaigns research victims’ crypto holdings through public blockchain analysis, then customize their approach with specific amounts and transaction details that appear legitimate. Chainalysis data indicates that phishing attacks resulted in approximately $295 million in losses in 2023, though the true figure is likely much higher as many victims never report these crimes.
Rug Pulls and Fake Tokens
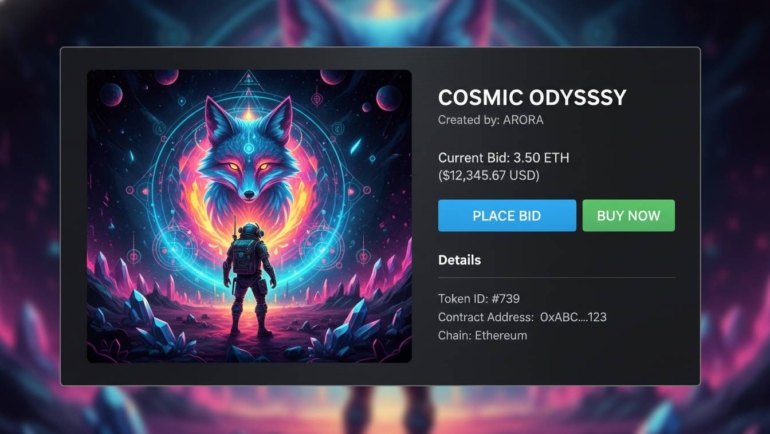
The decentralized finance (DeFi) ecosystem’s promise of permissionless innovation has a darker side: the rug pull. Scammers create seemingly legitimate cryptocurrency tokens, build hype through social media campaigns and influencer partnerships, attract significant investment, then drain liquidity pools and disappear. The token’s value collapses to zero within hours, leaving investors with worthless digital assets that cannot be sold.
Rug pulls typically follow a predictable pattern: anonymous developers, token contracts with hidden functions that allow mass minting or immediate selling by the creators, minimal audit documentation, and aggressive marketing that emphasizes “ground floor” opportunities. Research from CoinGecko found that approximately 7% of new token launches on decentralized exchanges in 2023 were identified as potential rug pulls, representing billions in potential investor losses.
Impersonation and Fake Support
Cryptocurrency’s technical complexity creates significant customer support needs, and scammers have built elaborate operations pretending to help. These fraudsters monitor social media for users discussing problems with specific exchanges or wallets, then reach out offering assistance through direct messages. Their “support” involves tricking victims into revealing recovery phrases, approving malicious smart contracts, or sending funds to “temporary wallets” for verification.
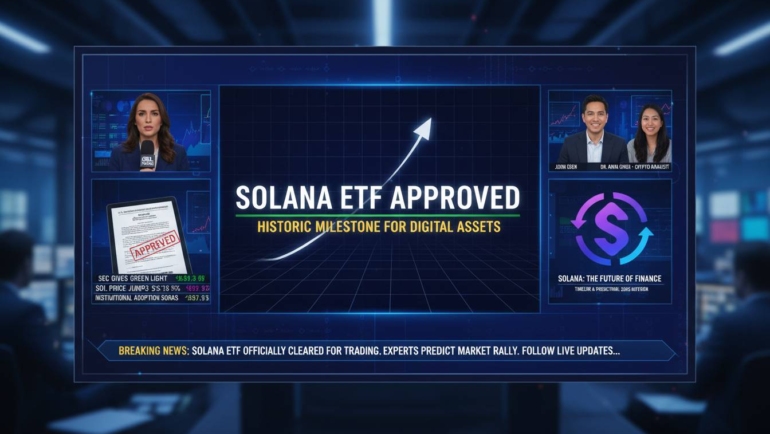
The rise of deepfake technology has added a new dimension to impersonation scams. Criminals now create video testimonials featuring AI-generated versions of celebrities or industry figures promising exclusive investment opportunities. These videos appear in social media feeds and YouTube advertisements, convincing viewers that trusted personalities are personally endorsing fraudulent schemes.
Red Flags: Warning Signs Every Investor Must Know
Recognizing scam indicators before investing saves far more money than any recovery effort. Several consistent warning signs appear across nearly every cryptocurrency scam, and developing automatic recognition for these patterns provides lasting protection.
Guaranteed returns represent the most reliable indicator of fraud. Cryptocurrency markets are inherently volatile—no legitimate investment can promise consistent daily profits regardless of market conditions. The mathematical reality of markets ensures that anyone claiming otherwise is either lying or operating illegally. Legitimate investment professionals provide risk disclosures and never guarantee outcomes.
Pressure tactics reveal desperation that honest businesses never exhibit. High-quality investment opportunities don’t require immediate action. Scammers create artificial scarcity through countdown timers, limited-time offers, and warnings about “closing windows.” Legitimate platforms welcome careful due diligence and provide ample information for informed decisions.
Unverifiable teams should immediately raise suspicion. Professional cryptocurrency projects feature identifiable founders with established track records, LinkedIn profiles, and history in the industry. Anonymous developers or teams using stock photos present obvious risks that sophisticated investors should never accept. Always verify team member identities through multiple independent sources.
Poor documentation distinguishes amateur operations from legitimate projects. Whitepapers that lack technical depth, tokenomics that don’t make mathematical sense, or missing audit reports from reputable security firms all signal elevated risk. The cryptocurrency space has established standards for transparency—projects refusing to meet these standards are communicating something important.
Unofficial communication channels create accountability problems that criminals exploit. Legitimate cryptocurrency companies maintain official domains, verified social media accounts, and established support systems. Contact through personal Telegram accounts, unofficial email addresses, or direct messages on social media eliminates the paper trail that enables legitimate dispute resolution.
Essential Security Practices for Crypto Investors
Protecting cryptocurrency requires combining technological solutions with behavioral discipline. No single measure provides complete security, but layered defenses dramatically reduce successful attack probability.
Wallet Security Fundamentals
The distinction between hot wallets (software-connected) and cold wallets (offline storage) defines security architecture for most investors. Hot wallets connected to the internet便利 for frequent trading but remain vulnerable to remote attacks. Cold wallets storing private keys offline provide far stronger protection but require physical access for transactions.
Hardware wallets from reputable manufacturers like Ledger or Trezor cost $50-250 and represent the single most effective investment for anyone holding significant cryptocurrency. These devices store private keys on specialized secure elements incapable of revealing keys to connected computers, enabling transaction signing without exposure. Even if your computer is completely compromised, hardware wallets protect underlying assets.
Recovery phrases—the lists of 12 or 24 words that regenerate wallet access—require physical security equal to cash holdings. Never store recovery phrases digitally, never share them with anyone, and never enter them into websites or apps that you didn’t deliberately navigate to yourself. The phrase provides complete access to your funds; anyone who obtains it owns your cryptocurrency.
Exchange Security Measures
Centralized exchanges remain the primary interaction point for most cryptocurrency investors, requiring specific security measures. Two-factor authentication using hardware security keys (YubiKey, Google Titan) provides substantially stronger protection than SMS codes or authenticator apps, both of which have demonstrated vulnerabilities to SIM swapping attacks.
Withdrawal whitelists limit damage from compromised accounts by restricting transfers to pre-approved addresses only. Enabling this feature means that even if attackers obtain full account access, they cannot transfer funds to their own wallets without additional verification steps. The minor inconvenience of adding new whitelist addresses provides massive security improvement.
Exchange account monitoring through email or SMS alerts for every login and transaction enables rapid response to unauthorized access. The earlier you detect a breach, the more options exist for preventing losses. Many exchanges now offer integrated notification systems that should be enabled regardless of other security measures.
Due Diligence Before Any Investment
Research requirements before cryptocurrency investment parallel those for traditional securities but require additional specialized checks. Confirm token contracts through blockchain explorers like Etherscan, verifying that addresses match official announcements and that no unusual functions exist in the code. Projects unwilling to share contract addresses provide immediate red flags.
Audit reports from established security firms like Certik, Trail of Bits, or OpenZeppelin identify vulnerabilities and suspicious code patterns. While audits don’t guarantee legitimacy, their absence in projects managing significant value indicates elevated risk tolerance. Cross-reference audit findings against project claims to identify discrepancies.
Community verification through established forums like BitcoinTalk (for older projects) or Reddit’s cryptocurrency communities provides grassroots perspective. Long-standing legitimate projects have documented histories and established community members who can answer questions. New projects with minimal community presence or only promotional content deserve skepticism.
What To Do If You’ve Been Scammed
Despite best precautions, some sophisticated attacks succeed. Response speed dramatically influences recovery potential, making rapid action essential.
Immediately document everything—screenshots of websites, messages, transaction hashes, wallet addresses involved, and any identifying information about scammers. This documentation supports both internal recovery efforts and potential law enforcement involvement. Blockchain analysis firms like Chainalysis and Elliptic can sometimes trace funds, and exchange compliance teams can sometimes freeze connected accounts if action occurs quickly enough.
File reports with relevant authorities including the FTC , FBI Internet Crime Complaint Center , and local police. While recovery rates remain low, reports create patterns that enable larger enforcement actions and help authorities track scam networks. The FBI’s Virtual Asset Unit has increased resources for cryptocurrency crime investigation, and several high-profile cases have resulted in significant recoveries.
Contact your bank or payment processor immediately if you used traditional payment methods alongside cryptocurrency. While cryptocurrency transfers cannot be reversed, credit card chargebacks or wire recall procedures may provide partial recovery if the transaction occurred recently. Document all communication with financial institutions for potential legal proceedings.
Frequently Asked Questions
How do I verify if a cryptocurrency project is legitimate before investing?
Legitimate projects provide verifiable team identities, published whitepapers with technical substance, audit reports from recognized security firms, and transparent token distribution details. Cross-reference all claims against independent sources—check blockchain explorers for actual contract behavior, review community discussions on established forums, and search for news coverage from reputable cryptocurrency publications. Projects that resist basic transparency verification should be avoided entirely.
Can cryptocurrency stolen in a scam be recovered?
Recovery is extremely difficult but not impossible in certain circumstances. If you can identify the wallet address where funds were sent, blockchain analysis firms may track subsequent movements and potentially identify exchanges where scammers subsequently moved or cashed out funds. Law enforcement has successfully recovered funds in several high-profile cases, particularly when victims report quickly and provide complete documentation. However, most stolen cryptocurrency is never recovered, making prevention far more valuable than attempted recovery.
Are there legitimate cryptocurrency investment opportunities, or should I avoid all crypto investing entirely?
Cryptocurrency itself is not a scam—millions of legitimate investors use digital assets for diverse purposes including portfolio diversification, decentralized finance participation, and transactions. The presence of widespread fraud doesn’t invalidate the underlying technology or legitimate projects. However, investors must approach cryptocurrency with the same due diligence applied to any alternative investment, understanding that regulatory protections and consumer protections remain significantly weaker than traditional financial markets.
What percentage of cryptocurrency investments end up being scams?
Precise percentages are difficult to determine because many scams operate privately and victims often don’t report losses. However, industry analyses suggest that approximately 1-2% of cryptocurrency users encounter scams, with higher rates among newer investors and those seeking unusually high returns. The Blockchain Intelligence Group estimates that investment fraud accounts for roughly one-third of all cryptocurrency crime by value, though the majority of individual incidents involve smaller amounts.
Building Sustainable Crypto Security Habits
Protecting your cryptocurrency requires treating security as an ongoing practice rather than a one-time setup. The threat landscape evolves constantly, with new scam techniques emerging as old ones become widely recognized. Subscribing to security-focused newsletters, following reputable cryptocurrency security researchers on social media, and regularly reviewing your own security practices creates resilience against evolving threats.
Your best defense combines knowledge, habits, and appropriate tools. Understanding how scams work eliminates the confusion that fraudsters exploit. Consistent security habits prevent the momentary lapses that lead to compromise. Quality security tools provide technical barriers that make successful attacks significantly more difficult. Together, these layers create protection that serves you regardless of which specific scams circulate at any given moment.
The cryptocurrency market will continue growing, attracting both legitimate innovation and criminal exploitation. By implementing the practices outlined in this guide, you position yourself to participate in legitimate crypto opportunities while avoiding the pitfalls that have cost investors billions. Remember: the best investment decision you can make is the one that keeps your money in your control.
This article provides general security guidance for cryptocurrency investors. Always conduct your own research and consult with qualified financial advisors before making investment decisions.