11Views 0Comments

Safest Way to Store Cryptocurrency: Expert Security Guide
Cryptocurrency ownership comes with unprecedented financial freedom, but it also carries unique responsibilities. Unlike traditional bank accounts protected by federal insurance and fraud protection, cryptocurrency funds exist in a decentralized system where you are your own bank. This makes understanding the safest way to store cryptocurrency not just important—it’s essential for protecting your digital assets from theft, loss, and human error.
The cryptocurrency landscape has evolved dramatically since Bitcoin’s creation in 2009, and so have the threats against holders. According to the FBI’s Internet Crime Report, cryptocurrency-related fraud exceeded $3.9 billion in losses in 2023 alone. Meanwhile, Chainalysis research indicates that approximately 20% of all Bitcoin in circulation—worth hundreds of billions of dollars—may be permanently lost due to forgotten passwords, lost hardware wallets, and other access issues. These statistics underscore a fundamental truth: the method you choose to store your cryptocurrency directly impacts its security.
This guide examines every viable storage method, from hardware wallets favored by security experts to emerging multi-signature solutions, providing you with the knowledge needed to make informed decisions about protecting your digital wealth.
Understanding Cryptocurrency Storage Fundamentals
Before examining specific storage methods, grasping the underlying technology is crucial. Cryptocurrency is not stored in a physical location or even a traditional file on your computer. Instead, your coins exist on the blockchain—a distributed public ledger—while your access to them is controlled by two cryptographic keys: a public key (which functions like an account number others can send money to) and a private key (which functions like a password authorizing transactions).
The private key represents absolute control over associated funds. Anyone who obtains your private key can transfer your cryptocurrency anywhere in the world, irreversibly. This fundamental reality shapes every security decision you’ll make. Storage methods ultimately differ in how they protect this critical piece of information from unauthorized access while ensuring you don’t lose it yourself.
Cryptocurrency storage falls into two primary categories: hot storage and cold storage. Hot storage refers to wallets connected to the internet, offering convenient access for transactions but presenting a larger attack surface for hackers. Cold storage means keeping your private keys offline, dramatically reducing remote theft risk while introducing challenges around accessibility and physical security.
The safest approach typically involves layering multiple security measures—a concept security professionals call “defense in depth.” Rather than relying on a single protection method, sophisticated holders combine different storage types based on how much they hold and how frequently they need to access those funds.
Hardware Wallets: The Gold Standard
Security experts consistently identify hardware wallets as the safest method for storing significant cryptocurrency holdings. These specialized devices store private keys in a secure hardware element—a dedicated chip designed to resist physical and logical tampering. When you need to authorize a transaction, the device performs cryptographic signing internally, ensuring your private key never leaves the device or touches an internet-connected computer.
The leading hardware wallet manufacturers include Ledger, Trezor, and ShapeShift’s Jack. Ledger, founded in 2014 and headquartered in Paris, has sold over 6 million devices worldwide as of 2024. Their devices feature a custom operating system called BOLOS and secure elements certified at Common Criteria EAL5+ level—the same certification used in banking cards and passports.
Trezor, produced by SatoshiLabs in the Czech Republic, pioneered the hardware wallet concept in 2014 with the original Trezor Model One. Their open-source approach allows security researchers to audit the device firmware, building trust through transparency. The current Model T features a touchscreen and supports over 1,000 cryptocurrencies.
When selecting a hardware wallet, purchasing directly from the manufacturer or authorized resellers is critical. Supply chain attacks—where compromised devices arrive pre-loaded with malicious software—have occurred in the cryptocurrency space. Always verify the device’s packaging integrity and initialize it following manufacturer instructions rather than accepting pre-configured devices.
The primary drawbacks of hardware wallets include cost (typically $79-$279), the learning curve for non-technical users, and the physical theft risk. If someone steals your device and obtains your PIN, they can access your funds. This vulnerability is why most experts recommend combining hardware wallets with BIP39 passphrases (additional words that create hidden wallets) and maintaining secure backups of your recovery seed.
Software Wallets: Convenience Versus Security
Software wallets—applications that run on computers, smartphones, or in web browsers—offer far greater convenience than hardware solutions but expose users to different risk categories. These wallets store private keys on internet-connected devices, making them vulnerable to malware, phishing attacks, and exploits.
Desktop wallets like Exodus, Electrum, and Bitcoin Core store keys locally on your computer. While this eliminates some web-based risks, any malware infecting your system can potentially capture keystrokes, access files, or take screenshots revealing your keys or seed phrases. Electrum, created in 2011, has remained popular among Bitcoin users for its lightweight design and advanced features like multi-signature support and hardware wallet integration.
Mobile wallets provide the ultimate accessibility, allowing you to send and receive cryptocurrency from anywhere. Trust Wallet (acquired by Binance in 2019) supports over 100 blockchains and claims millions of users. BlueWallet specializes in Bitcoin with features like Lightning Network support and robust backup options. These mobile applications face unique threats including malicious apps mimicking legitimate wallets, SIM-swapping attacks targeting phone numbers used for two-factor authentication, and device vulnerabilities.
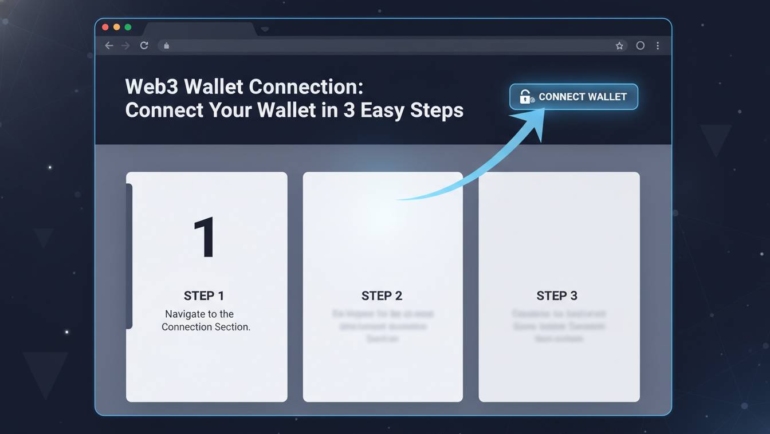
Browser extension wallets like MetaMask have exploded in popularity alongside decentralized finance (DeFi) applications. MetaMask alone serves over 30 million monthly active users. These wallets interact with web3 applications directly, meaning every website you visit potentially has opportunity to attempt phishing attacks or request signatures that could drain your wallet. Security consciousness—carefully verifying website URLs, never sharing seed phrases, and using hardware wallets for significant holdings—becomes non-negotiable with these tools.
The fundamental advice from security professionals is clear: use software wallets only for small amounts you can afford to lose. Consider them “spending wallets” rather than “savings wallets.” Keep the bulk of your holdings in hardware wallets or other cold storage solutions, transferring funds to software wallets only when preparing to make transactions.
Paper Wallets: Old School Security
Paper wallets represent the ultimate cold storage concept—completely offline, immune to digital attacks, and requiring no specialized hardware beyond a printer. A paper wallet is simply your private key and corresponding public address printed on paper, often with QR codes for easy scanning.
Generating a paper wallet requires extreme care. Using online generators exposes your keys to the generating website, completely defeating the security purpose. The proper method involves downloading wallet generation software (like bitaddress.org for Bitcoin) onto an air-gapped computer—never connected to the internet—generating keys offline, and printing using a wired printer (not wireless) also disconnected from networks. Some security experts recommend using dedicated computers for this purpose, never used for any other activity.
Once generated, paper wallets must be stored physically. This introduces considerations like fire protection, water damage, theft, and loss. Many holders laminate their paper wallets and store them in safe deposit boxes, home safes, or secret physical locations. The old saying “not your keys, not your crypto” applies perfectly here—if you hold a paper wallet, you truly control the keys, with no intermediary service that could fail or be compromised.
The major drawback of paper wallets is usability. To spend funds, you must import or sweep the private key into a software or hardware wallet, after which the paper wallet becomes empty. This process can be confusing for newcomers and introduces momentary digital exposure. Additionally, paper degrades over time, and human error during generation or storage can result in permanent fund loss.
Despite these limitations, paper wallets remain popular among long-term holders (“HODLers”) who value absolute control and minimal attack surface. When properly generated and stored, they resist every form of digital attack known to date.
Exchange Wallets: When Convenience Trumps Security
Cryptocurrency exchanges like Coinbase, Binance, and Kraken provide hosted wallets as part of their service. When you create an account and deposit cryptocurrency, the exchange holds the private keys while you control access through their interface. This model offers tremendous convenience: easy buying and selling, password recovery options, and customer support if problems arise.
However, this convenience comes with significant trade-offs. You don’t truly own your cryptocurrency in the same sense—you own a claim against the exchange. If the exchange experiences financial problems, regulatory action, or hacking, your funds could be at risk. The collapse of FTX in November 2022 demonstrated this clearly, as billions in customer funds disappeared when the exchange could not meet withdrawal demands.
Exchanges remain prime targets for hackers. Mt. Gox, once handling 70% of all Bitcoin transactions, lost approximately 850,000 Bitcoin (worth billions at current prices) in attacks spanning 2011-2014. More recently, the Ronin Network hack in March 2022 resulted in $625 million in losses. Even security-conscious exchanges face determined attackers, and no platform can guarantee absolute protection.
Best practices if using exchange wallets include: enabling all available security features (two-factor authentication, anti-phishing codes, withdrawal whitelists), using unique passwords not reused elsewhere, storing only actively-traded funds on exchanges, and withdrawing holdings to personal wallets when not actively trading. Many experienced holders treat exchanges as transaction venues rather than storage solutions, moving funds to personal control within hours of any purchase.
Multi-Signature Storage Solutions
Multi-signature (multisig) wallets represent an advanced security architecture requiring multiple private keys to authorize transactions. Rather than single-point-of-failure access, these wallets distribute control across several keys—perhaps requiring 2-of-3 or 3-of-5 signatures for any transaction.
This approach provides powerful protection against both theft and loss. If a 2-of-3 multisig wallet requires any two keys, losing one key doesn’t result in fund loss. Similarly, stealing one key provides insufficient access for thieves. Corporate treasuries, family offices, and significant individual holdings benefit enormously from this structure.
Hardware wallet manufacturer Ledger offers multi-signature capabilities through their Ledger Vault platform, designed for institutional clients. Casa provides multi-signature solutions for individuals, offering setups ranging from 3-of-5 to 5-of-7 key configurations. Keys can be distributed geographically—in safe deposit boxes in different cities, with different family members, or across different security setups.
The complexity of multisig solutions makes them overkill for small holdings but increasingly attractive as portfolio values grow. Setting up proper multi-signature wallets requires careful planning: how many keys total, how many required for transactions, where each key will be stored, who will hold keys, and what procedures exist for key recovery or inheritance.
Security Best Practices Every Holder Should Know
Beyond selecting a storage method, implementing consistent security practices determines actual protection. These principles apply regardless of which wallet type you choose.
Never share your seed phrase. The 12 or 24 words that generate your wallet’s private keys represent complete fund access. No legitimate service, support representative, or person needs to know these words. Treat them like passwords—if someone obtains them, they own your cryptocurrency. Write them on paper (not digitally), store them separately from your wallet device, and consider splitting across multiple secure locations.
Verify everything. Before sending significant cryptocurrency, verify addresses character-by-character. Malware can modify copied addresses, redirecting funds to attacker-controlled wallets. Double-check URLs when accessing wallet or exchange websites—phishing sites often use similar-looking domains.
Use unique, strong passwords. Every cryptocurrency-related account deserves a unique, complex password. Password managers make this manageable. Enable two-factor authentication using authenticator apps or hardware tokens rather than SMS (which remains vulnerable to SIM-swapping attacks).
Test with small amounts first. When using new wallets, software, or procedures, send tiny test transactions before moving significant funds. This verifies everything works correctly and ensures you understand the process.
Plan for the unexpected. What happens to your cryptocurrency if you become incapacitated or die? Unlike bank accounts with established inheritance procedures, cryptocurrency holdings can become permanently inaccessible without proper planning. Consider who should have access, how they’ll obtain necessary information, and whether you need legal documents specifying digital asset inheritance.
Frequently Asked Questions
What is the safest wallet for beginners?
For beginners holding modest amounts, hardware wallets from established manufacturers like Ledger or Trezor offer the best balance of security and usability. The initial learning curve pays dividends in peace of mind. Start with smaller purchases while learning the system, and only add more significant holdings once you’re comfortable with the process.
Should I keep all my cryptocurrency in one wallet?
Most security experts recommend diversifying storage rather than concentrating everything in one location. This could mean using a hardware wallet for long-term holdings, a software wallet for smaller active amounts, and perhaps multi-signature solutions for very large portfolios. Distribution protects against single points of failure—whether technical, procedural, or physical.
Can cryptocurrency be stolen from a hardware wallet?
While hardware wallets dramatically reduce remote theft risk, they’re not invulnerable. If an attacker obtains your physical device AND your PIN, they can access funds. This is why using BIP39 passphrases (creating additional words beyond your seed that form hidden wallets) and maintaining proper physical security matters. Also, always verify transaction details on the hardware wallet screen before confirming—malicious computer software could attempt to alter recipient addresses.
What happens if I lose my hardware wallet?
Losing a hardware wallet doesn’t mean losing your cryptocurrency, provided you maintain proper seed phrase backups. Your 12-24 word recovery seed can restore all funds to a new device. This is why the seed phrase backup—stored securely in separate locations—truly represents your ultimate security. Without it, a lost device becomes permanently inaccessible.
Is cold storage really necessary?
Cold storage becomes increasingly important as holdings grow. For small amounts (under $1,000), the convenience of software or mobile wallets may outweigh minimal risks. For anything meaningful—say, over a few thousand dollars—hardware wallets or paper wallets provide substantially superior protection. Many serious holders consider anything above certain thresholds to require cold storage regardless of convenience costs.
How often should I check my stored cryptocurrency?
Monthly verification is reasonable for most holders—confirming your balances and that all storage methods remain intact. However, daily checking provides no additional security and can lead to unnecessary worry. Focus on knowing your backup systems work: test restoring from seed phrases periodically if possible, and ensure your physical storage locations remain secure and unchanged.
Conclusion
The safest way to store cryptocurrency ultimately depends on your specific situation: how much you hold, how often you need to access it, your technical comfort level, and your threat model. For most holders, a hardware wallet from a reputable manufacturer like Ledger or Trezor, combined with proper seed phrase backup procedures, provides the optimal balance of security and usability.
Remember that cryptocurrency security operates on uncomfortable absolutes. Unlike traditional finance where institutions bear security burdens and provide recovery mechanisms, you carry complete responsibility. The techniques that protect digital assets—cold storage, seed phrase management, multi-signature architecture—require deliberate action and ongoing attention.
Start with whichever storage method matches your current holdings and comfort level, then reassess as your portfolio grows. The cryptocurrency space continues evolving, with new security solutions emerging regularly. Stay informed, remain cautious, and never stop treating your digital assets with the serious protection they deserve.